Perkoon vs Phishly
Side-by-side comparison to help you choose the right product.
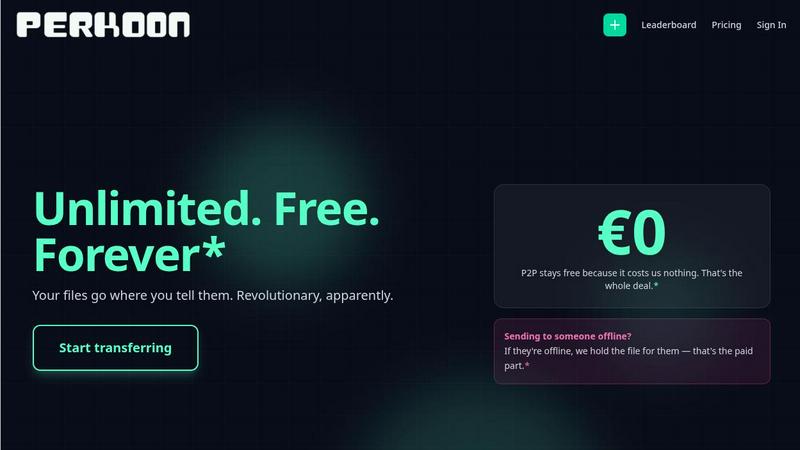
Perkoon enables free unlimited peer-to-peer file transfers with no signup needed, keeping your files private and secure.
Last updated: March 4, 2026
Phishly
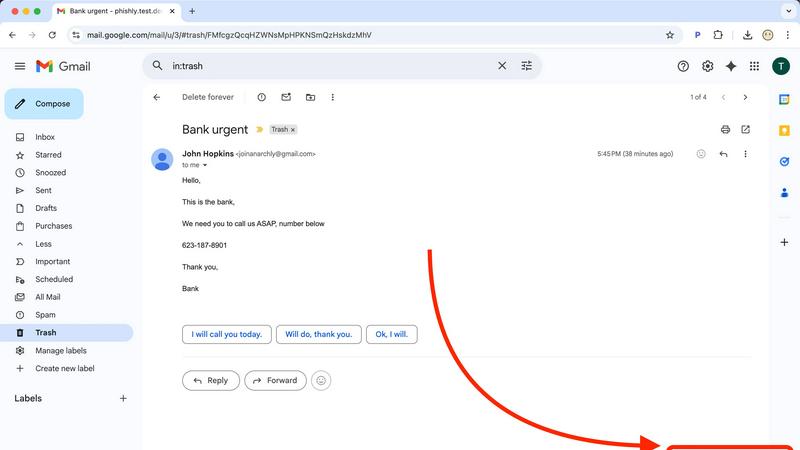
Phishly instantly detects phishing emails with AI to secure your inbox at scale.
Visual Comparison
Perkoon
Phishly
Feature Comparison
Perkoon
Peer-to-Peer (P2P) File Transfer
Perkoon’s flagship feature allows users to send files directly to one another without the need for an account or server intervention. This P2P technology means unlimited file sizes and complete privacy, as files are transferred directly between browsers during real-time sessions.
Encrypted Cloud Storage
For occasions when recipients are offline, Perkoon provides a secure cloud storage option. This feature ensures that files are encrypted on the server, making them accessible only to intended recipients while covering the costs of server maintenance transparently.
Automation and AI Integration
Recognizing the growing role of AI in everyday tasks, Perkoon includes built-in tools for automation. This allows AI agents to interact with the service directly, streamlining the file transfer process without needing screen-scraping methods, which enhances usability and efficiency.
Unique Referral Program
Perkoon incentivizes users to share the service through its referral program. By sharing a unique link, users can earn additional storage space for themselves and their referrals, creating a community-driven ecosystem that rewards sharing and collaboration.
Phishly
AI-Powered Deep Scan
Our core AI engine conducts a multi-layered forensic analysis of every email you submit. It goes beyond simple link checking to examine the email's DNA: dissecting domain reputation, header information for spoofing, grammatical inconsistencies, and the nuanced language of social engineering like urgency, fear, or too-good-to-be-true offers. This comprehensive scan ensures even the most cleverly disguised phishing attempts are identified before they can cause harm.
Clear-Cut Risk Assessment & Explanation
Phishly cuts through the noise with straightforward, color-coded risk ratings: Safe (Green), Medium Risk (Yellow), and High Risk (Red). But we don't just give you a score. Each result includes a detailed breakdown explaining why the email was flagged, pointing out specific suspicious elements. This educational component empowers users to become more security-savvy over time, building a stronger human firewall within your organization.
Privacy-First, On-Demand Analysis
Your privacy is non-negotiable. Unlike systems that scan all your emails automatically, Phishly operates on a strict, user-initiated model. We only analyze the specific email you open and choose to scan or the text you paste into our web tool. This ensures maximum control and transparency, giving you powerful security insights without ever compromising the confidentiality of your broader inbox or communications.
Seamless Gmail Integration & Web Tool
Security should fit into your workflow, not disrupt it. Our lightweight Chrome extension integrates directly into your Gmail interface, adding a simple "Scan with Phishly" button for one-click analysis. For emails outside Gmail or for team-wide scrutiny, our companion web tool allows you to paste any email content for an instant check. This dual-approach flexibility ensures protection wherever you work.
Use Cases
Perkoon
Quick File Sharing for Teams
Teams working on collaborative projects can utilize Perkoon for instant file sharing. By leveraging the P2P feature, team members can exchange large files in real time without worrying about size restrictions or complicated sign-up processes.
Secure Personal File Transfers
Individuals looking to transfer sensitive documents can rely on Perkoon’s encrypted cloud storage for added security. This feature is especially useful for sharing personal information, ensuring that files are only accessible to the intended recipient.
Automation for Developers
Developers can integrate Perkoon into their workflows using the CLI tool and automation features. This allows for seamless file transfers between development environments and production systems, enhancing productivity while maintaining security.
Community Engagement and Growth
Using the referral program, users can engage their networks while benefiting from additional storage. This makes Perkoon not just a file transfer service but a platform that grows through community involvement, rewarding users for sharing the experience.
Phishly
Empowering Non-Technical Teams
Small businesses and startups often lack dedicated IT security staff. Phishly democratizes protection by giving every employee—from sales to operations—a simple, one-click tool to verify suspicious emails. This instantly elevates your organization's security posture, reduces risk, and prevents costly breaches without requiring complex training or security expertise.
Verifying Urgent Financial or Login Requests
Phishing attacks often impersonate banks, payment platforms, or IT departments with urgent requests to "verify your account" or "update your payment details." Before clicking any link or replying with sensitive information, users can scan the email with Phishly. Our AI detects spoofed sender addresses and suspicious links, providing immediate peace of mind or a critical warning.
Screening Client & Partner Communications
Freelancers and agencies receive emails from various new contacts and potential clients. Phishly acts as a vetting tool for these external communications, helping to identify potential scams disguised as project inquiries or partnership opportunities. This protects your business from business email compromise (BEC) scams and fraudulent requests.
Building a Security-Conscious Culture
By using Phishly's explanatory reports in team discussions or security briefings, leaders can turn individual scans into collective learning moments. Regularly reviewing why an email was flagged as risky helps train employees to recognize red flags independently, fostering a proactive, security-minded culture that scales with your company's growth.
Overview
About Perkoon
Perkoon is a revolutionary file transfer service designed with simplicity and privacy at its core. It caters to individuals and businesses tired of conventional file sharing methods that impose artificial limits and unnecessary sign-ups. Perkoon eliminates these barriers by enabling hassle-free file transfers directly between users. Built on peer-to-peer (P2P) technology, Perkoon allows users to send files directly from browser to browser when both parties are online, ensuring no size limits and no intermediary servers involved. This unique approach guarantees that your data remains private and secure. For situations where recipients are offline, Perkoon offers encrypted cloud storage as a paid feature, providing users with flexibility without compromising security. Additionally, Perkoon is designed for the modern age of AI, offering automation tools and a simple CLI tool for seamless integration with AI agents. With a commitment to providing a straightforward and powerful solution, Perkoon is the answer for those seeking a trustworthy file transfer service.
About Phishly
In today's digital-first world, your inbox is the frontline of your business's security. Phishly is the intelligent, proactive shield you need, designed to scale with your ambition. We are an AI-powered phishing detection platform that transforms how individuals and growing businesses defend against sophisticated email threats. Available as a seamless Chrome extension for Gmail and a versatile web tool, Phishly puts enterprise-grade security analysis directly in your hands without the enterprise complexity or cost. Simply open any email and click "Scan with Phishly" or paste suspicious content onto our website for an instant, deep-dive analysis. Our advanced AI engine meticulously scans for a comprehensive range of phishing indicators—from suspicious domains and spoofed sender addresses to urgent language and psychological social engineering tactics. It then delivers a clear, actionable risk assessment: Safe, Medium Risk, or High Risk, each accompanied by a detailed, plain-English explanation. Built with a foundational commitment to privacy, we only analyze emails you explicitly choose to scan, ensuring your data remains yours. Phishly is the essential growth tool for entrepreneurs, freelancers, and SMBs who demand simple, powerful protection that empowers their team and secures their trajectory. It's free to use, requires zero technical knowledge, and delivers the instant clarity you need to make confident decisions and keep moving forward.
Frequently Asked Questions
Perkoon FAQ
How does Perkoon ensure my files remain private?
Perkoon uses P2P technology for file transfers, meaning your files do not pass through centralized servers. This ensures total privacy, as no one, including Perkoon, has access to your transferred data.
What happens if the recipient is offline?
If the recipient is offline, Perkoon offers encrypted cloud storage to hold the file safely until the recipient is available to download it. This ensures that your files are secure and accessible at their convenience.
Can I use Perkoon on any browser?
Perkoon works seamlessly with Chrome, Edge, and Brave browsers without any limitations. However, users of Firefox and Safari may encounter some restrictions due to the way these browsers handle P2P connections.
Is there a cost associated with using Perkoon?
The P2P file transfer service is completely free, as it incurs no costs for Perkoon to operate. However, if you choose to use the encrypted cloud storage feature when the recipient is offline, that will come with a fee to cover server costs.
Phishly FAQ
How does Phishly protect my privacy?
Phishly is built on a principle of explicit user consent and minimal data access. Our Chrome extension only analyzes the specific email you have open and actively choose to scan. We do not continuously monitor, read, or store emails from your inbox. The web tool only analyzes the text you paste into it. We are designed to be a tool for your scrutiny, not a surveillance platform.
What makes Phishly different from my email provider's spam filter?
Traditional spam filters operate silently in the background and primarily catch bulk, low-effort spam. Phishly is a targeted, on-demand analysis tool designed to catch sophisticated phishing emails that often bypass standard filters because they appear to come from trusted sources. It gives you active control and detailed forensic insight at the moment of doubt, acting as a second layer of defense.
Is technical knowledge required to use Phishly?
Absolutely not. Phishly is designed for complete simplicity. Installing the Chrome extension takes one click from the Web Store. From there, using it is as simple as opening an email and clicking the "Scan with Phishly" button. The results are presented in plain language with clear risk indicators, making it accessible for everyone, regardless of their technical background.
What does the "Medium Risk" assessment mean?
A "Medium Risk" rating indicates that the email contains some suspicious characteristics but not a definitive phishing signature. This could include a slightly mismatched sender domain, unusual but not malicious language, or links to newly registered domains. The detailed explanation will specify these factors, allowing you to exercise caution—perhaps by contacting the supposed sender through a verified channel before proceeding.
