iGPT vs Threat Watch
Side-by-side comparison to help you choose the right product.
iGPT gives enterprise AI agents instant, secure context from messy email data.
Last updated: February 28, 2026
Threat Watch
Scale your security instantly with proactive, actionable cyber risk insights.
Last updated: March 1, 2026
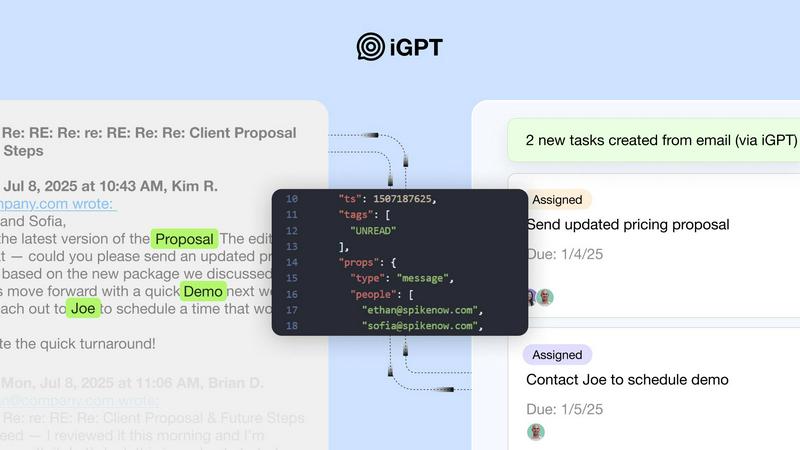
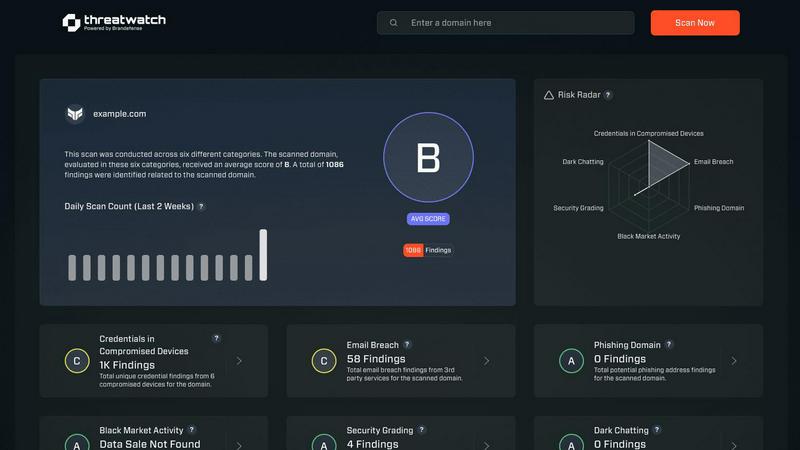
Visual Comparison
iGPT
Threat Watch
Feature Comparison
iGPT
Unified Intelligent Endpoint
Replace complex, multi-step retrieval pipelines with a single, powerful API call. iGPT consolidates the entire process—from natural language query to cited, structured output—into one unified endpoint. This eliminates the need for separate systems for parsing, vector storage, and prompt chaining, radically simplifying integration and accelerating development cycles for engineering teams.
Hybrid Retrieval with Context Shaping
iGPT employs a sophisticated hybrid retrieval system that combines semantic understanding, keyword matching, and configurable filters, all scored and reranked in a single operation. It then automatically optimizes and shapes the context window for your LLM, delivering the most relevant information without any manual prompt tuning or engineering overhead.
Automated Thread Reconstruction & Attachment Processing
The API intelligently rebuilds complete email threads across time, participants, and related messages. It simultaneously processes attachments—extracting text, data, and structure from documents, PDFs, and spreadsheets—and integrates this content into the conversational context, providing a holistic view of every interaction.
Enterprise-Grade Security & Compliance
Built with zero data training, zero data retention, and OAuth-only processing with strict Role-Based Access Control (RBAC). Each inference is processed in memory; inputs, prompts, and outputs are never stored. This ensures full data sovereignty and a complete audit trail, making it safe for the most sensitive enterprise communications and compliance requirements.
Threat Watch
Real-Time Attack Surface Monitoring
Threat Watch provides a live, unified view of your organization's entire external digital footprint. It continuously discovers and analyzes assets, domains, and infrastructure for vulnerabilities and misconfigurations, ensuring you always know your exposure level. This proactive surveillance moves you beyond periodic scans to constant vigilance, essential for fast-moving companies adding new services and technologies weekly.
Compromised Credential Intelligence
This feature actively scans breach databases and the dark web for your company's employee credentials. It instantly alerts you if email addresses and passwords associated with your domain are found in leaked data sets, enabling you to enforce password resets before those credentials can be used in credential-stuffing or account takeover attacks, securing your primary gateways.
Phishing & Impersonation Detection
Threat Watch monitors for phishing campaigns and domain impersonations targeting your brand and employees. It identifies newly registered lookalike domains, malicious copies of your login pages, and phishing kits using your logos. This early warning system allows you to take down threats before they trick your team or damage your customer trust.
Automated Security Health Scoring
Get an immediate, comprehensible snapshot of your cybersecurity posture with an automated health score. Threat Watch evaluates critical categories like credential exposure, phishing risk, and dark web mentions, consolidating complex data into a single, actionable metric. This empowers leaders to make fast, informed decisions and track improvement over time as they scale.
Use Cases
iGPT
Autonomous Email Assistants
Build intelligent agents that can draft, prioritize, summarize, and act on email with full historical and attachment context. These assistants can autonomously handle routine communication, flag urgent items, and manage inbox workflows, dramatically increasing productivity and ensuring nothing slips through the cracks.
Intelligent Workflow Automation
Transform email threads into structured, actionable data. Automatically extract tasks, deadlines, approvals, and decisions from conversations. Identify stalled processes or pending actions and integrate them directly into project management tools, CRMs, or ticketing systems to keep workflows moving.
Customer Support Copilots
Empower support teams with agents that instantly reconstruct the full customer story. By analyzing long email chains, shifting tones, and all related attachments, these copilots provide support reps with immediate, comprehensive context, enabling faster, more personalized, and more effective customer resolutions.
CRM & Deal Intelligence Agents
Supercharge sales and CRM platforms by extracting critical insights directly from email threads. Automatically identify deal momentum, key decisions, stakeholder sentiment, action owners, and important dates buried in communications, providing real-time intelligence to forecast accurately and close deals faster.
Threat Watch
Proactive Risk Management for Scaling Startups
As a startup rapidly adopts new SaaS tools, cloud infrastructure, and hires employees, its attack surface explodes. Threat Watch provides the overwhelmed, lean security team with automated, continuous oversight. It identifies the most critical exposures—like an employee's reused password in a recent breach—allowing them to fix high-impact issues first and maintain security without slowing down product development cycles.
Enabling Secure Enterprise Growth & Mergers
For modern enterprises undergoing mergers, acquisitions, or rapid expansion, understanding the security posture of new assets is critical. Threat Watch can be deployed to instantly assess the external security health of a target company or new division, revealing unknown vulnerabilities, compromised credentials, and dark web exposures before they become part of your liability.
Empowering IT Leaders with Actionable Intelligence
IT Directors and CISOs need to communicate risk to the board in clear business terms. Threat Watch’s unified dashboard and health score translate technical threats into strategic insights. Leaders can demonstrate due diligence, showcase ROI on security initiatives, and advocate for resources based on clear, data-driven pictures of the organization's cyber risk landscape.
Preventing Account Takeover and Data Breaches
By continuously monitoring for compromised employee credentials on the dark web and in breach databases, Threat Watch acts as an early warning system. Security teams receive immediate alerts when credentials are found, allowing them to force password resets and implement multi-factor authentication (MFA) proactively, shutting down the most common vector for major breaches before it's exploited.
Overview
About iGPT
iGPT is the definitive email intelligence API engineered for the age of AI agents and scalable enterprise workflows. It solves a critical bottleneck: while email is the central nervous system of business communication, it has historically been a black box for AI—messy, unstructured, and laden with sensitive data. iGPT transforms this chaos into a secure, queryable source of truth. It acts as a powerful, unified gateway that allows agentic systems and applications to deeply understand and leverage email conversations and attachments with unprecedented context and speed. Designed for engineering teams and product builders, its core value is radical simplification. You bypass the entire complex pipeline of parsing, chunking, indexing, and prompt engineering. With a single API call, iGPT handles real-time ingestion, hybrid retrieval, thread reconstruction, and context shaping, delivering cited, structured answers in seconds. This enables enterprises to confidently deploy autonomous agents and intelligent features that automate tasks, extract insights, and drive decisions directly from the communication layer where real work happens, all within a framework built for enterprise-grade security and compliance from the ground up.
About Threat Watch
Threat Watch is the proactive cybersecurity intelligence platform engineered for the unique pace and challenges of scaling startups and modern, growth-focused enterprises. In a digital landscape where threats evolve faster than traditional security cycles, reactive measures are a recipe for risk. Threat Watch delivers a strategic advantage by providing a unified, real-time dashboard of your organization's cyber health. It continuously scans and analyzes your entire digital attack surface—from assets and vulnerabilities to critical exposures—transforming overwhelming, fragmented threat data into a clear, actionable picture. Built for IT leaders and security teams who must enable business velocity without compromising on defense, Threat Watch automates critical assessments. It delivers instant, prioritized insights into compromised credentials, breached employee accounts, phishing risks, and dark web exposures. This empowers teams to identify, contextualize, and mitigate risks with unprecedented speed, turning cybersecurity from a perceived cost center into a core driver of resilient, confident growth. It's not just monitoring; it's the intelligence layer that allows your business to scale securely.
Frequently Asked Questions
iGPT FAQ
How does iGPT handle data privacy and security?
iGPT is architected for enterprise trust. It operates on a zero data training and zero data retention policy. Your data is never used to train models or improve services. All processing happens in memory per request and is never persisted to disk. Access is strictly controlled via OAuth and RBAC, ensuring data never leaves your company's control.
What is the "Context Engineering Framework (CEF)"?
The Context Engineering Framework refers to the sophisticated, multi-stage pipeline iGPT runs internally. It encompasses real-time ingestion, hybrid retrieval, thread reconstruction, and intelligent context shaping. Different CEF "tiers" (like cef-1-normal) allow you to balance speed, cost, and depth of analysis for each query to optimize performance.
How quickly can I integrate and start using iGPT?
Integration is designed for speed. With a ready-to-use SDK, a live playground for testing, and comprehensive documentation, developers can connect email sources and make their first productive API call in minutes, not days. The unified endpoint means there's no complex infrastructure to set up or maintain.
Can iGPT process attachments within emails?
Absolutely. A core capability of iGPT is its deep attachment processing. It automatically extracts and indexes text, data, and structural information from a wide range of file types—including PDFs, documents, and spreadsheets—and seamlessly incorporates this content into the context of the email thread for a complete intelligence picture.
Threat Watch FAQ
How does Threat Watch discover my company's assets and exposures?
Threat Watch uses a combination of non-intrusive, external scanning techniques and active intelligence gathering. It discovers your publicly facing digital assets like domains, IP ranges, and cloud instances. Simultaneously, it continuously queries a vast array of breach databases, dark web forums, and phishing kit repositories for any data linked to your company's domains and brand identifiers, all without requiring internal network access.
Is Threat Watch suitable for a company with no dedicated security team?
Absolutely. Threat Watch is designed to democratize advanced cybersecurity intelligence. Its automated health score and prioritized, plain-language alerts make complex threats understandable for IT generalists, founders, or operations leaders. It provides clear, actionable steps, allowing smaller teams to effectively manage risk and build a security foundation as they grow.
What kind of alerts will I receive, and how are they prioritized?
You will receive real-time alerts for critical discoveries such as your employee credentials found in a new data breach, a lookalike domain registered to phish your customers, or a high-severity vulnerability on your web server. Threats are prioritized based on severity, potential business impact, and ease of exploitation, ensuring your team focuses on what matters most to your operational security.
How does Threat Watch help with compliance and vendor risk?
Threat Watch provides continuous evidence of your proactive security monitoring, which supports frameworks like SOC 2, ISO 27001, and GDPR. The platform's assessment capabilities can also be used for third-party vendor risk management. You can gain an instant external view of a potential vendor's security hygiene before integration, ensuring your partnerships don't introduce unnecessary risk.
Alternatives
iGPT Alternatives
iGPT is a definitive email intelligence API, transforming messy email data into a secure, queryable source of truth for AI agents and enterprise workflows. It belongs to the business intelligence category, specifically designed to unlock the operational insights trapped within business communication. Teams often explore alternatives for various reasons, such as specific budget constraints, the need for different integration capabilities, or a requirement for features outside a core email intelligence focus. The search for the right tool is a natural part of scaling a tech stack. When evaluating options, prioritize solutions that offer true real-time data synchronization, robust security built for enterprise use, and a developer experience that radically simplifies pipeline complexity. The goal is to find a platform that turns communication data into a reliable asset for automation without creating new technical debt.
Threat Watch Alternatives
Threat Watch is a proactive cybersecurity intelligence platform in the business intelligence category. It transforms complex threat data into a clear, actionable picture of your cyber health, empowering scaling companies to move fast and securely. Users often explore alternatives to find the perfect fit for their unique scaling journey. Common reasons include budget alignment, specific feature requirements like deeper integration capabilities, or the need for a platform tailored to a different stage of company growth. When evaluating alternatives, focus on core value. Look for solutions that offer real-time, actionable insights, automate critical security assessments, and provide a unified view of your risk. The right platform should turn security from a reactive cost into a proactive driver of resilient growth.
