Pursuit vs Threat Watch
Side-by-side comparison to help you choose the right product.
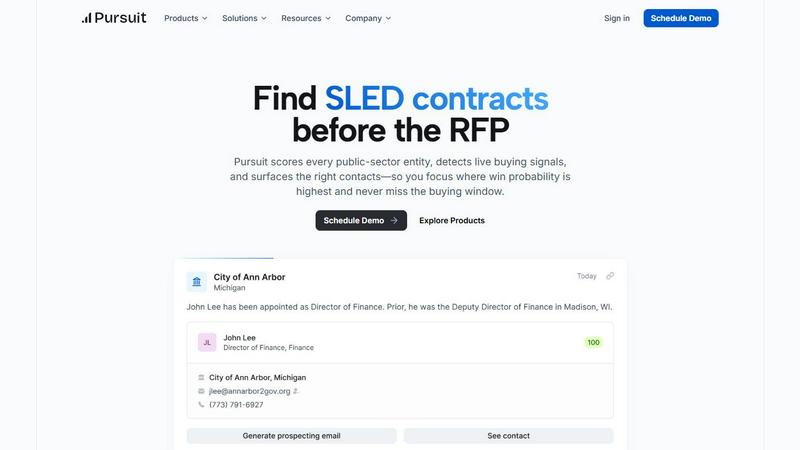
Pursuit
Pursuit leverages AI to uncover public sector contract opportunities months early, positioning you as the frontrunner.
Last updated: February 28, 2026
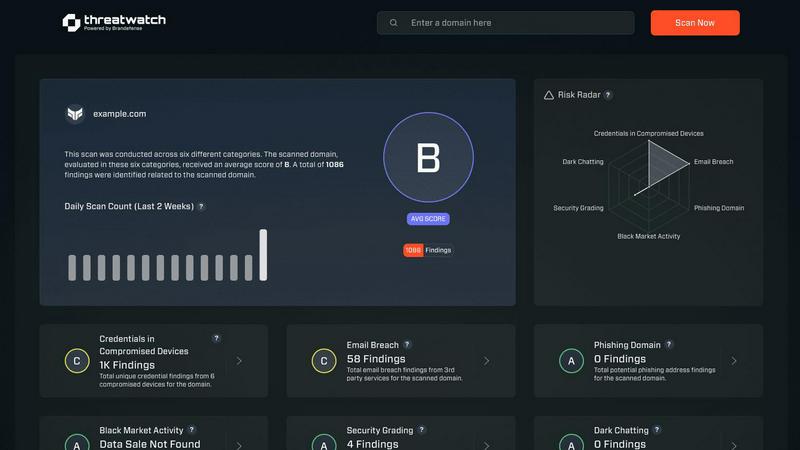
Threat Watch
Scale your security instantly with proactive, actionable cyber risk insights.
Last updated: March 1, 2026
Visual Comparison
Pursuit
Threat Watch
Feature Comparison
Pursuit
Proactive Buying Signals
Pursuit surfaces critical buying signals 6 to 18 months before RFPs are issued, enabling your sales team to act early and position themselves as incumbents. This foresight allows organizations to engage in meaningful conversations with potential clients ahead of the competition.
Real-Time Data Integration
With native integrations to platforms like Salesforce and HubSpot, Pursuit ensures that data flows seamlessly into your existing stack. This feature guarantees that your team has access to accurate and up-to-date information, enhancing decision-making and operational efficiency.
Comprehensive Opportunity Tracking
Pursuit continuously monitors over 110,000 entities, providing insights into unique procurement processes and budget cycles. This comprehensive tracking equips your team with the knowledge needed to navigate the complex landscape of public sector sales effectively.
Cross-Functional Intelligence Sharing
The platform facilitates shared intelligence across your go-to-market (GTM) team. From marketing to sales and customer success, everyone operates on the same data, ensuring that signals flow seamlessly and fostering collaboration across departments.
Threat Watch
Real-Time Attack Surface Monitoring
Threat Watch provides a live, unified view of your organization's entire external digital footprint. It continuously discovers and analyzes assets, domains, and infrastructure for vulnerabilities and misconfigurations, ensuring you always know your exposure level. This proactive surveillance moves you beyond periodic scans to constant vigilance, essential for fast-moving companies adding new services and technologies weekly.
Compromised Credential Intelligence
This feature actively scans breach databases and the dark web for your company's employee credentials. It instantly alerts you if email addresses and passwords associated with your domain are found in leaked data sets, enabling you to enforce password resets before those credentials can be used in credential-stuffing or account takeover attacks, securing your primary gateways.
Phishing & Impersonation Detection
Threat Watch monitors for phishing campaigns and domain impersonations targeting your brand and employees. It identifies newly registered lookalike domains, malicious copies of your login pages, and phishing kits using your logos. This early warning system allows you to take down threats before they trick your team or damage your customer trust.
Automated Security Health Scoring
Get an immediate, comprehensible snapshot of your cybersecurity posture with an automated health score. Threat Watch evaluates critical categories like credential exposure, phishing risk, and dark web mentions, consolidating complex data into a single, actionable metric. This empowers leaders to make fast, informed decisions and track improvement over time as they scale.
Use Cases
Pursuit
Maximize Pre-RFP Engagement
By leveraging Pursuit's proactive buying signals, organizations can engage potential clients well before RFPs are released. This positions them strategically as trusted advisors, leading to increased win rates and stronger relationships.
Streamline Sales Operations
Sales leaders can utilize Pursuit to gain visibility into which team members are engaging with specific signals. This clarity allows for better territory management and resource allocation, ultimately maximizing the effectiveness of sales operations.
Enhance Account-Based Marketing Efforts
Marketers can build account-based marketing (ABM) campaigns based on real-time buying signals. By aligning marketing efforts with budget approvals and new initiatives, organizations can improve their conversion rates significantly.
Improve Customer Success Management
Pursuit alerts customer success teams about upcoming contract renewals and potential churn signals. This proactive approach empowers teams to engage clients at critical moments, enhancing retention and satisfaction.
Threat Watch
Proactive Risk Management for Scaling Startups
As a startup rapidly adopts new SaaS tools, cloud infrastructure, and hires employees, its attack surface explodes. Threat Watch provides the overwhelmed, lean security team with automated, continuous oversight. It identifies the most critical exposures—like an employee's reused password in a recent breach—allowing them to fix high-impact issues first and maintain security without slowing down product development cycles.
Enabling Secure Enterprise Growth & Mergers
For modern enterprises undergoing mergers, acquisitions, or rapid expansion, understanding the security posture of new assets is critical. Threat Watch can be deployed to instantly assess the external security health of a target company or new division, revealing unknown vulnerabilities, compromised credentials, and dark web exposures before they become part of your liability.
Empowering IT Leaders with Actionable Intelligence
IT Directors and CISOs need to communicate risk to the board in clear business terms. Threat Watch’s unified dashboard and health score translate technical threats into strategic insights. Leaders can demonstrate due diligence, showcase ROI on security initiatives, and advocate for resources based on clear, data-driven pictures of the organization's cyber risk landscape.
Preventing Account Takeover and Data Breaches
By continuously monitoring for compromised employee credentials on the dark web and in breach databases, Threat Watch acts as an early warning system. Security teams receive immediate alerts when credentials are found, allowing them to force password resets and implement multi-factor authentication (MFA) proactively, shutting down the most common vector for major breaches before it's exploited.
Overview
About Pursuit
Pursuit is an innovative AI-powered intelligence platform that revolutionizes the way companies engage with the public sector. Designed specifically for fast-growing government contractors, technology vendors, and professional services firms, Pursuit transforms the traditionally slow and opaque government sales cycle into a proactive, data-driven growth engine. By continuously scanning over 90,000 state, local, education, and special district entities, Pursuit provides actionable intelligence that helps sales teams focus their efforts on opportunities with the highest win probabilities. The platform empowers organizations to build their pipelines before Requests for Proposals (RFPs) are issued, ensuring they are well-positioned as incumbents rather than outsiders. Pursuit effectively removes the friction associated with public sector sales, enabling teams to scale their revenue predictably and serve the public sector more effectively.
About Threat Watch
Threat Watch is the proactive cybersecurity intelligence platform engineered for the unique pace and challenges of scaling startups and modern, growth-focused enterprises. In a digital landscape where threats evolve faster than traditional security cycles, reactive measures are a recipe for risk. Threat Watch delivers a strategic advantage by providing a unified, real-time dashboard of your organization's cyber health. It continuously scans and analyzes your entire digital attack surface—from assets and vulnerabilities to critical exposures—transforming overwhelming, fragmented threat data into a clear, actionable picture. Built for IT leaders and security teams who must enable business velocity without compromising on defense, Threat Watch automates critical assessments. It delivers instant, prioritized insights into compromised credentials, breached employee accounts, phishing risks, and dark web exposures. This empowers teams to identify, contextualize, and mitigate risks with unprecedented speed, turning cybersecurity from a perceived cost center into a core driver of resilient, confident growth. It's not just monitoring; it's the intelligence layer that allows your business to scale securely.
Frequently Asked Questions
Pursuit FAQ
How does Pursuit help in identifying buying signals?
Pursuit analyzes data from a vast array of state and local entities to surface buying signals well in advance of RFPs. This allows teams to engage opportunities at the right time, significantly improving win rates.
Can Pursuit integrate with existing CRM systems?
Yes, Pursuit offers native integrations with popular CRM platforms like Salesforce and HubSpot. This ensures that your data is automatically enriched and updated, streamlining your sales processes.
What types of organizations benefit from Pursuit?
Pursuit is designed for fast-growing government contractors, technology vendors, and professional services firms that target the public sector. Any organization seeking to enhance their public sector sales efforts will find value in Pursuit.
How does Pursuit enhance collaboration across teams?
By providing shared intelligence across marketing, sales, and customer success, Pursuit ensures that all teams operate from the same data set. This promotes alignment and collaboration, leading to improved overall performance.
Threat Watch FAQ
How does Threat Watch discover my company's assets and exposures?
Threat Watch uses a combination of non-intrusive, external scanning techniques and active intelligence gathering. It discovers your publicly facing digital assets like domains, IP ranges, and cloud instances. Simultaneously, it continuously queries a vast array of breach databases, dark web forums, and phishing kit repositories for any data linked to your company's domains and brand identifiers, all without requiring internal network access.
Is Threat Watch suitable for a company with no dedicated security team?
Absolutely. Threat Watch is designed to democratize advanced cybersecurity intelligence. Its automated health score and prioritized, plain-language alerts make complex threats understandable for IT generalists, founders, or operations leaders. It provides clear, actionable steps, allowing smaller teams to effectively manage risk and build a security foundation as they grow.
What kind of alerts will I receive, and how are they prioritized?
You will receive real-time alerts for critical discoveries such as your employee credentials found in a new data breach, a lookalike domain registered to phish your customers, or a high-severity vulnerability on your web server. Threats are prioritized based on severity, potential business impact, and ease of exploitation, ensuring your team focuses on what matters most to your operational security.
How does Threat Watch help with compliance and vendor risk?
Threat Watch provides continuous evidence of your proactive security monitoring, which supports frameworks like SOC 2, ISO 27001, and GDPR. The platform's assessment capabilities can also be used for third-party vendor risk management. You can gain an instant external view of a potential vendor's security hygiene before integration, ensuring your partnerships don't introduce unnecessary risk.
Alternatives
Pursuit Alternatives
Pursuit is an innovative AI-powered intelligence platform tailored for companies targeting the public sector. It falls under the category of business intelligence, aiming to transform the sluggish government sales cycle into a dynamic and data-driven growth engine. By providing actionable insights and live buying signals, Pursuit empowers sales teams to identify and engage with opportunities before they arise, ensuring they never miss a critical buying window. Users often seek alternatives to Pursuit for various reasons, including pricing considerations, specific feature requirements, or compatibility with existing platforms. When exploring alternatives, it's essential to evaluate the robustness of the data provided, the responsiveness of the platform to changing market conditions, and how well the solution aligns with your organization's unique needs. Finding the right fit will enable your team to maximize their public sector sales potential.
Threat Watch Alternatives
Threat Watch is a proactive cybersecurity intelligence platform in the business intelligence category. It transforms complex threat data into a clear, actionable picture of your cyber health, empowering scaling companies to move fast and securely. Users often explore alternatives to find the perfect fit for their unique scaling journey. Common reasons include budget alignment, specific feature requirements like deeper integration capabilities, or the need for a platform tailored to a different stage of company growth. When evaluating alternatives, focus on core value. Look for solutions that offer real-time, actionable insights, automate critical security assessments, and provide a unified view of your risk. The right platform should turn security from a reactive cost into a proactive driver of resilient growth.
