Deeploy vs Threat Watch
Side-by-side comparison to help you choose the right product.

Deeploy
Deeploy empowers organizations to govern and scale AI confidently while managing risks and ensuring compliance.
Last updated: March 1, 2026
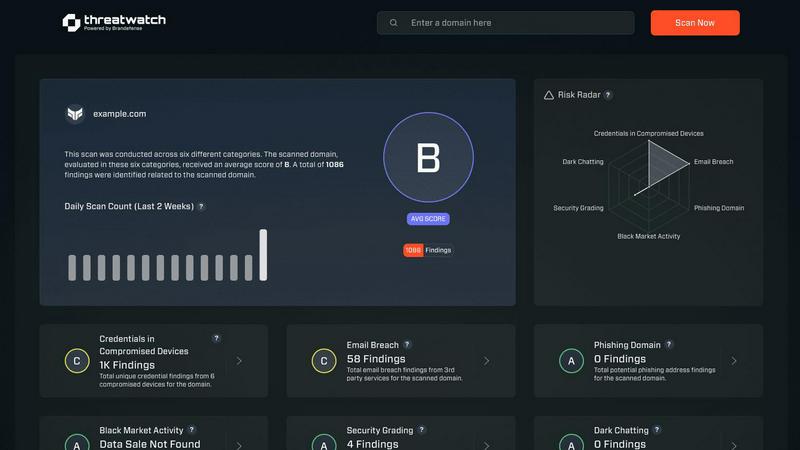
Threat Watch
Scale your security instantly with proactive, actionable cyber risk insights.
Last updated: March 1, 2026
Visual Comparison
Deeploy
Threat Watch
Feature Comparison
Deeploy
AI Discovery and Onboarding
Deeploy provides comprehensive visibility across your AI landscape, allowing organizations to discover, onboard, and manage every AI system from a single interface. This feature eliminates blind spots and integrates seamlessly with any MLOps or GenAI platform, ensuring centralized control without the hassle of migration.
Control Frameworks
This feature simplifies compliance with AI regulations through guided workflows that make navigating complex requirements straightforward. Users can choose from default control frameworks like ISO 42001 and NIST AI RMF or create custom frameworks tailored to their specific needs, ensuring accountability and risk classification within minutes.
Control Implementation
Deeploy turns governance frameworks into actionable controls that engineers can easily follow. By providing clear, enforceable requirements for every AI system, it accelerates compliance by up to 90% with ready-made templates and automated evidence collection, reducing manual labor and streamlining processes.
Real-Time Monitoring
Stay ahead of potential issues with real-time monitoring that detects performance drops or model drift before they affect users. Deeploy sends instant alerts for anomalies, enabling proactive management and maintaining compliance with added tracing and guardrails for LLM outputs, ensuring your AI operates smoothly.
Threat Watch
Real-Time Attack Surface Monitoring
Threat Watch provides a live, unified view of your organization's entire external digital footprint. It continuously discovers and analyzes assets, domains, and infrastructure for vulnerabilities and misconfigurations, ensuring you always know your exposure level. This proactive surveillance moves you beyond periodic scans to constant vigilance, essential for fast-moving companies adding new services and technologies weekly.
Compromised Credential Intelligence
This feature actively scans breach databases and the dark web for your company's employee credentials. It instantly alerts you if email addresses and passwords associated with your domain are found in leaked data sets, enabling you to enforce password resets before those credentials can be used in credential-stuffing or account takeover attacks, securing your primary gateways.
Phishing & Impersonation Detection
Threat Watch monitors for phishing campaigns and domain impersonations targeting your brand and employees. It identifies newly registered lookalike domains, malicious copies of your login pages, and phishing kits using your logos. This early warning system allows you to take down threats before they trick your team or damage your customer trust.
Automated Security Health Scoring
Get an immediate, comprehensible snapshot of your cybersecurity posture with an automated health score. Threat Watch evaluates critical categories like credential exposure, phishing risk, and dark web mentions, consolidating complex data into a single, actionable metric. This empowers leaders to make fast, informed decisions and track improvement over time as they scale.
Use Cases
Deeploy
Regulated Industries
Organizations in heavily regulated sectors like finance and healthcare can leverage Deeploy to ensure they meet stringent compliance requirements while scaling their AI systems. This helps maintain trust and transparency with stakeholders and customers.
AI Innovation Acceleration
Deeploy empowers teams to innovate rapidly while ensuring that their AI systems are governed appropriately. By automating compliance and monitoring, organizations can focus on developing new AI capabilities without the fear of regulatory repercussions.
Multi-Vendor AI Management
For businesses utilizing AI solutions from various vendors, Deeploy serves as a centralized governance hub that provides oversight and compliance across all platforms. This integration fosters a cohesive AI strategy and mitigates risks associated with vendor-specific systems.
Continuous Improvement in AI Models
Data scientists can utilize Deeploy to iterate quickly on their production models, ensuring that they receive feedback on AI predictions. With built-in explainability, organizations can continuously refine their models, enhancing performance and user satisfaction.
Threat Watch
Proactive Risk Management for Scaling Startups
As a startup rapidly adopts new SaaS tools, cloud infrastructure, and hires employees, its attack surface explodes. Threat Watch provides the overwhelmed, lean security team with automated, continuous oversight. It identifies the most critical exposures—like an employee's reused password in a recent breach—allowing them to fix high-impact issues first and maintain security without slowing down product development cycles.
Enabling Secure Enterprise Growth & Mergers
For modern enterprises undergoing mergers, acquisitions, or rapid expansion, understanding the security posture of new assets is critical. Threat Watch can be deployed to instantly assess the external security health of a target company or new division, revealing unknown vulnerabilities, compromised credentials, and dark web exposures before they become part of your liability.
Empowering IT Leaders with Actionable Intelligence
IT Directors and CISOs need to communicate risk to the board in clear business terms. Threat Watch’s unified dashboard and health score translate technical threats into strategic insights. Leaders can demonstrate due diligence, showcase ROI on security initiatives, and advocate for resources based on clear, data-driven pictures of the organization's cyber risk landscape.
Preventing Account Takeover and Data Breaches
By continuously monitoring for compromised employee credentials on the dark web and in breach databases, Threat Watch acts as an early warning system. Security teams receive immediate alerts when credentials are found, allowing them to force password resets and implement multi-factor authentication (MFA) proactively, shutting down the most common vector for major breaches before it's exploited.
Overview
About Deeploy
Deeploy is the essential AI governance infrastructure tailored for organizations that are serious about scaling their artificial intelligence initiatives. It transforms the chaotic landscape of AI into a manageable, compliant, and strategic asset, ensuring organizations can navigate the complexities of AI deployment without incurring operational, reputational, or regulatory risks. Deeploy centralizes oversight, compliance, and monitoring across all AI systems, whether developed in-house, sourced from third-party vendors, or integrated within other applications. Designed for enterprises and regulated industries, its main value proposition lies in providing clarity and control. By offering complete visibility into the AI landscape and enforcing governance frameworks that are practical for engineers, Deeploy enables businesses to accelerate compliance with evolving regulations like the EU AI Act and ISO 42001. With features like automated evidence collection and built-in explainability, Deeploy positions itself as a catalyst for responsible AI innovation, transitioning governance from a potential bottleneck to a powerful enabler of growth and safety.
About Threat Watch
Threat Watch is the proactive cybersecurity intelligence platform engineered for the unique pace and challenges of scaling startups and modern, growth-focused enterprises. In a digital landscape where threats evolve faster than traditional security cycles, reactive measures are a recipe for risk. Threat Watch delivers a strategic advantage by providing a unified, real-time dashboard of your organization's cyber health. It continuously scans and analyzes your entire digital attack surface—from assets and vulnerabilities to critical exposures—transforming overwhelming, fragmented threat data into a clear, actionable picture. Built for IT leaders and security teams who must enable business velocity without compromising on defense, Threat Watch automates critical assessments. It delivers instant, prioritized insights into compromised credentials, breached employee accounts, phishing risks, and dark web exposures. This empowers teams to identify, contextualize, and mitigate risks with unprecedented speed, turning cybersecurity from a perceived cost center into a core driver of resilient, confident growth. It's not just monitoring; it's the intelligence layer that allows your business to scale securely.
Frequently Asked Questions
Deeploy FAQ
What types of organizations benefit from using Deeploy?
Deeploy is designed for enterprises and regulated industries that are looking to scale their AI initiatives responsibly. It is especially beneficial for organizations in finance, healthcare, and other sectors where compliance is critical.
How does Deeploy ensure compliance with AI regulations?
Deeploy automates compliance processes through guided workflows, enabling organizations to implement control frameworks like ISO 42001 and NIST AI RMF. This not only simplifies compliance but also accelerates it through automated evidence collection.
Can Deeploy integrate with existing AI systems?
Yes, Deeploy is built to connect seamlessly with any MLOps or GenAI platform. This ensures that organizations can discover and manage all AI systems from one central interface without the need for extensive migration efforts.
How does real-time monitoring work in Deeploy?
Deeploy’s real-time monitoring feature continuously tracks AI performance and sends instant alerts for any anomalies or performance declines. This proactive approach allows organizations to address potential issues before they impact users or lead to compliance violations.
Threat Watch FAQ
How does Threat Watch discover my company's assets and exposures?
Threat Watch uses a combination of non-intrusive, external scanning techniques and active intelligence gathering. It discovers your publicly facing digital assets like domains, IP ranges, and cloud instances. Simultaneously, it continuously queries a vast array of breach databases, dark web forums, and phishing kit repositories for any data linked to your company's domains and brand identifiers, all without requiring internal network access.
Is Threat Watch suitable for a company with no dedicated security team?
Absolutely. Threat Watch is designed to democratize advanced cybersecurity intelligence. Its automated health score and prioritized, plain-language alerts make complex threats understandable for IT generalists, founders, or operations leaders. It provides clear, actionable steps, allowing smaller teams to effectively manage risk and build a security foundation as they grow.
What kind of alerts will I receive, and how are they prioritized?
You will receive real-time alerts for critical discoveries such as your employee credentials found in a new data breach, a lookalike domain registered to phish your customers, or a high-severity vulnerability on your web server. Threats are prioritized based on severity, potential business impact, and ease of exploitation, ensuring your team focuses on what matters most to your operational security.
How does Threat Watch help with compliance and vendor risk?
Threat Watch provides continuous evidence of your proactive security monitoring, which supports frameworks like SOC 2, ISO 27001, and GDPR. The platform's assessment capabilities can also be used for third-party vendor risk management. You can gain an instant external view of a potential vendor's security hygiene before integration, ensuring your partnerships don't introduce unnecessary risk.
Alternatives
Deeploy Alternatives
Deeploy is a cutting-edge AI governance infrastructure tailored for organizations aiming to scale artificial intelligence effectively and responsibly. It operates within the Business Intelligence category, providing essential oversight and compliance tools that transform the chaotic landscape of AI into a well-governed, strategic asset. Users often seek alternatives to Deeploy for various reasons, including pricing concerns, specific feature requirements, or compatibility with existing platforms. When considering alternatives, it’s crucial to evaluate the platform's ability to centralize AI oversight, enforce governance frameworks, and provide real-time monitoring to ensure compliance and mitigate risks.
Threat Watch Alternatives
Threat Watch is a proactive cybersecurity intelligence platform in the business intelligence category. It transforms complex threat data into a clear, actionable picture of your cyber health, empowering scaling companies to move fast and securely. Users often explore alternatives to find the perfect fit for their unique scaling journey. Common reasons include budget alignment, specific feature requirements like deeper integration capabilities, or the need for a platform tailored to a different stage of company growth. When evaluating alternatives, focus on core value. Look for solutions that offer real-time, actionable insights, automate critical security assessments, and provide a unified view of your risk. The right platform should turn security from a reactive cost into a proactive driver of resilient growth.
