Fusedash vs Threat Watch
Side-by-side comparison to help you choose the right product.
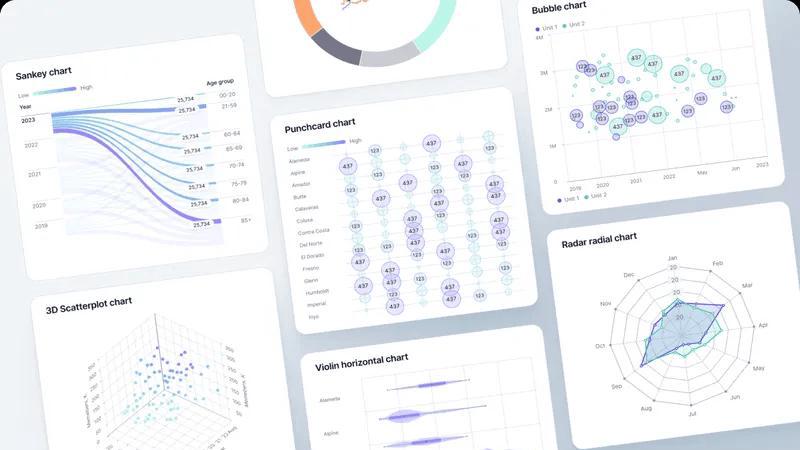
Fusedash transforms raw data into intuitive dashboards and charts, empowering teams to act on insights instantly.
Last updated: March 4, 2026
Threat Watch
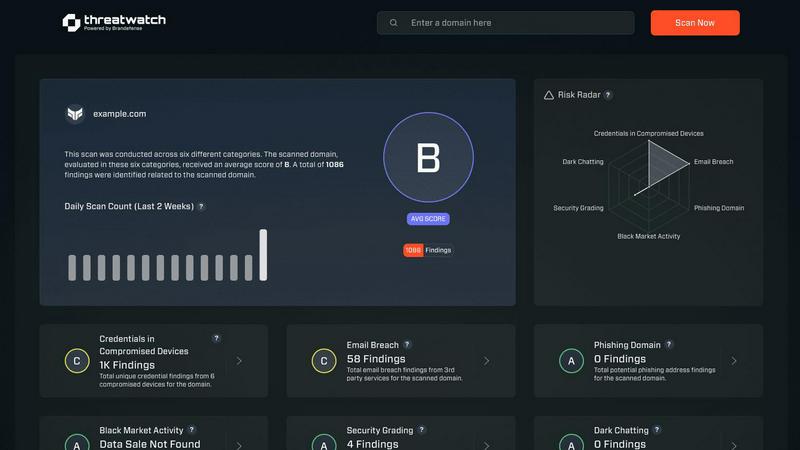
Scale your security instantly with proactive, actionable cyber risk insights.
Last updated: March 1, 2026
Visual Comparison
Fusedash
Threat Watch
Feature Comparison
Fusedash
Flexible Views
Fusedash offers the capability to create customized dashboards, charts, maps, and report-style views tailored for different audiences. This flexibility allows stakeholders to see only the most relevant data without unnecessary back-and-forth communication, streamlining the decision-making process.
AI Chart Generator
With the AI Chart Generator, users can swiftly create clear and impactful visuals from datasets in mere minutes. The tool assists in selecting the most appropriate chart types, applying necessary comparisons, and refining labels to ensure the visuals convey the intended narrative effectively.
One Workspace for Dashboards and Reporting
Fusedash consolidates dashboards and reporting into a single platform, providing context alongside performance views. This feature enhances clarity by combining data visualization with storytelling, helping teams understand changes and their implications while reducing inconsistencies in reporting.
Smart AI Chat
The Smart AI Chat feature empowers users to engage with their data in natural language. Users can ask questions, explore data breakdowns, and receive tailored suggestions for metrics and visualizations, making data exploration intuitive and collaborative.
Threat Watch
Real-Time Attack Surface Monitoring
Threat Watch provides a live, unified view of your organization's entire external digital footprint. It continuously discovers and analyzes assets, domains, and infrastructure for vulnerabilities and misconfigurations, ensuring you always know your exposure level. This proactive surveillance moves you beyond periodic scans to constant vigilance, essential for fast-moving companies adding new services and technologies weekly.
Compromised Credential Intelligence
This feature actively scans breach databases and the dark web for your company's employee credentials. It instantly alerts you if email addresses and passwords associated with your domain are found in leaked data sets, enabling you to enforce password resets before those credentials can be used in credential-stuffing or account takeover attacks, securing your primary gateways.
Phishing & Impersonation Detection
Threat Watch monitors for phishing campaigns and domain impersonations targeting your brand and employees. It identifies newly registered lookalike domains, malicious copies of your login pages, and phishing kits using your logos. This early warning system allows you to take down threats before they trick your team or damage your customer trust.
Automated Security Health Scoring
Get an immediate, comprehensible snapshot of your cybersecurity posture with an automated health score. Threat Watch evaluates critical categories like credential exposure, phishing risk, and dark web mentions, consolidating complex data into a single, actionable metric. This empowers leaders to make fast, informed decisions and track improvement over time as they scale.
Use Cases
Fusedash
Marketing Analytics
Marketing teams can leverage Fusedash to track campaign performance and customer engagement metrics in real time. The ability to customize views ensures that marketers can focus on the data that matters most, leading to data-driven decisions that enhance campaign effectiveness.
Financial Reporting
Finance departments can utilize Fusedash to streamline the creation of financial reports and dashboards. By defining KPIs and using consistent metrics, teams can eliminate discrepancies and ensure that all stakeholders have access to accurate, up-to-date financial information.
Operations Management
Operations teams can benefit from Fusedash by monitoring key operational metrics and performance indicators. The platform's real-time monitoring capabilities allow teams to identify bottlenecks and optimize processes, promoting efficiency and productivity.
Sales Performance Tracking
Sales teams can use Fusedash to visualize sales data and performance metrics. With the ability to drill down into specific segments and time periods, sales professionals can better understand trends, identify opportunities, and strategize for future growth.
Threat Watch
Proactive Risk Management for Scaling Startups
As a startup rapidly adopts new SaaS tools, cloud infrastructure, and hires employees, its attack surface explodes. Threat Watch provides the overwhelmed, lean security team with automated, continuous oversight. It identifies the most critical exposures—like an employee's reused password in a recent breach—allowing them to fix high-impact issues first and maintain security without slowing down product development cycles.
Enabling Secure Enterprise Growth & Mergers
For modern enterprises undergoing mergers, acquisitions, or rapid expansion, understanding the security posture of new assets is critical. Threat Watch can be deployed to instantly assess the external security health of a target company or new division, revealing unknown vulnerabilities, compromised credentials, and dark web exposures before they become part of your liability.
Empowering IT Leaders with Actionable Intelligence
IT Directors and CISOs need to communicate risk to the board in clear business terms. Threat Watch’s unified dashboard and health score translate technical threats into strategic insights. Leaders can demonstrate due diligence, showcase ROI on security initiatives, and advocate for resources based on clear, data-driven pictures of the organization's cyber risk landscape.
Preventing Account Takeover and Data Breaches
By continuously monitoring for compromised employee credentials on the dark web and in breach databases, Threat Watch acts as an early warning system. Security teams receive immediate alerts when credentials are found, allowing them to force password resets and implement multi-factor authentication (MFA) proactively, shutting down the most common vector for major breaches before it's exploited.
Overview
About Fusedash
Fusedash is an innovative AI-powered data visualization platform that revolutionizes the way teams interact with their data. Designed for organizations seeking clarity and efficiency, Fusedash consolidates data from multiple sources into a single, cohesive workspace. Users can create decision-ready dashboards, interactive charts, detailed maps, and narrative reports, all without the hassle of reconstructing logic across disparate tools. With its primary focus on consistency, Fusedash allows teams to define key metrics and KPIs once and reuse them across various reports and views, ensuring that everyone—from leadership to operational teams—has access to the same trusted numbers. This platform is perfect for teams looking to eliminate tedious manual reporting cycles and resolve conflicting data narratives. By enabling real-time data monitoring and deep-dive analytics, Fusedash empowers users to not only track performance but also understand the underlying factors driving results. Its integrated AI features, such as natural language data chat and smart visualization assistance, make data exploration and reporting faster and more accessible, turning raw data into actionable insights that drive organizational alignment and informed decision-making.
About Threat Watch
Threat Watch is the proactive cybersecurity intelligence platform engineered for the unique pace and challenges of scaling startups and modern, growth-focused enterprises. In a digital landscape where threats evolve faster than traditional security cycles, reactive measures are a recipe for risk. Threat Watch delivers a strategic advantage by providing a unified, real-time dashboard of your organization's cyber health. It continuously scans and analyzes your entire digital attack surface—from assets and vulnerabilities to critical exposures—transforming overwhelming, fragmented threat data into a clear, actionable picture. Built for IT leaders and security teams who must enable business velocity without compromising on defense, Threat Watch automates critical assessments. It delivers instant, prioritized insights into compromised credentials, breached employee accounts, phishing risks, and dark web exposures. This empowers teams to identify, contextualize, and mitigate risks with unprecedented speed, turning cybersecurity from a perceived cost center into a core driver of resilient, confident growth. It's not just monitoring; it's the intelligence layer that allows your business to scale securely.
Frequently Asked Questions
Fusedash FAQ
What types of data sources can I connect to Fusedash?
Fusedash supports various data sources, including CSV uploads, API connections, and public datasets. This versatility allows users to bring together diverse data into one unified platform for comprehensive analysis.
How does Fusedash ensure data consistency across reports?
Fusedash enables users to define key metrics and KPIs once and reuse them across all dashboards and reports. This standardization ensures that all teams are aligned and reviewing the same trusted data, minimizing discrepancies.
Can I customize the visualizations in Fusedash?
Absolutely! Fusedash allows users to customize visualizations extensively, including layout designs, filters, and time ranges. This ensures that each dashboard or report is tailored specifically to its audience's needs.
Is support available for new users of Fusedash?
Yes, Fusedash provides support for new users, including resources to help with onboarding and tutorials for using the platform effectively. Users can also request a demo to get a personalized introduction to its features and capabilities.
Threat Watch FAQ
How does Threat Watch discover my company's assets and exposures?
Threat Watch uses a combination of non-intrusive, external scanning techniques and active intelligence gathering. It discovers your publicly facing digital assets like domains, IP ranges, and cloud instances. Simultaneously, it continuously queries a vast array of breach databases, dark web forums, and phishing kit repositories for any data linked to your company's domains and brand identifiers, all without requiring internal network access.
Is Threat Watch suitable for a company with no dedicated security team?
Absolutely. Threat Watch is designed to democratize advanced cybersecurity intelligence. Its automated health score and prioritized, plain-language alerts make complex threats understandable for IT generalists, founders, or operations leaders. It provides clear, actionable steps, allowing smaller teams to effectively manage risk and build a security foundation as they grow.
What kind of alerts will I receive, and how are they prioritized?
You will receive real-time alerts for critical discoveries such as your employee credentials found in a new data breach, a lookalike domain registered to phish your customers, or a high-severity vulnerability on your web server. Threats are prioritized based on severity, potential business impact, and ease of exploitation, ensuring your team focuses on what matters most to your operational security.
How does Threat Watch help with compliance and vendor risk?
Threat Watch provides continuous evidence of your proactive security monitoring, which supports frameworks like SOC 2, ISO 27001, and GDPR. The platform's assessment capabilities can also be used for third-party vendor risk management. You can gain an instant external view of a potential vendor's security hygiene before integration, ensuring your partnerships don't introduce unnecessary risk.
Alternatives
Fusedash Alternatives
Fusedash is an innovative AI-powered data visualization platform that falls into the Analytics & Data and Business Intelligence categories. It empowers teams to transform raw data into clear, actionable insights through unified dashboards and interactive reports. Users commonly seek alternatives to Fusedash for various reasons, such as pricing constraints, specific feature requirements, or the need for a platform that better integrates with existing workflows. When evaluating alternatives, it's essential to consider factors like ease of use, scalability, the depth of data visualization options, and the level of customer support provided.
Threat Watch Alternatives
Threat Watch is a proactive cybersecurity intelligence platform in the business intelligence category. It transforms complex threat data into a clear, actionable picture of your cyber health, empowering scaling companies to move fast and securely. Users often explore alternatives to find the perfect fit for their unique scaling journey. Common reasons include budget alignment, specific feature requirements like deeper integration capabilities, or the need for a platform tailored to a different stage of company growth. When evaluating alternatives, focus on core value. Look for solutions that offer real-time, actionable insights, automate critical security assessments, and provide a unified view of your risk. The right platform should turn security from a reactive cost into a proactive driver of resilient growth.
